Build Your Agency’s Next Breakthrough on a Zero Trust Foundation
Zero Trust isn’t a single solution or piece of hardware. It’s a set of principles that governs the way we approach cybersecurity. The intended outcome of a Zero Trust model is for trusted identities to get access to the applications, systems, networks and data based on their roles and what they need to perform their jobs.
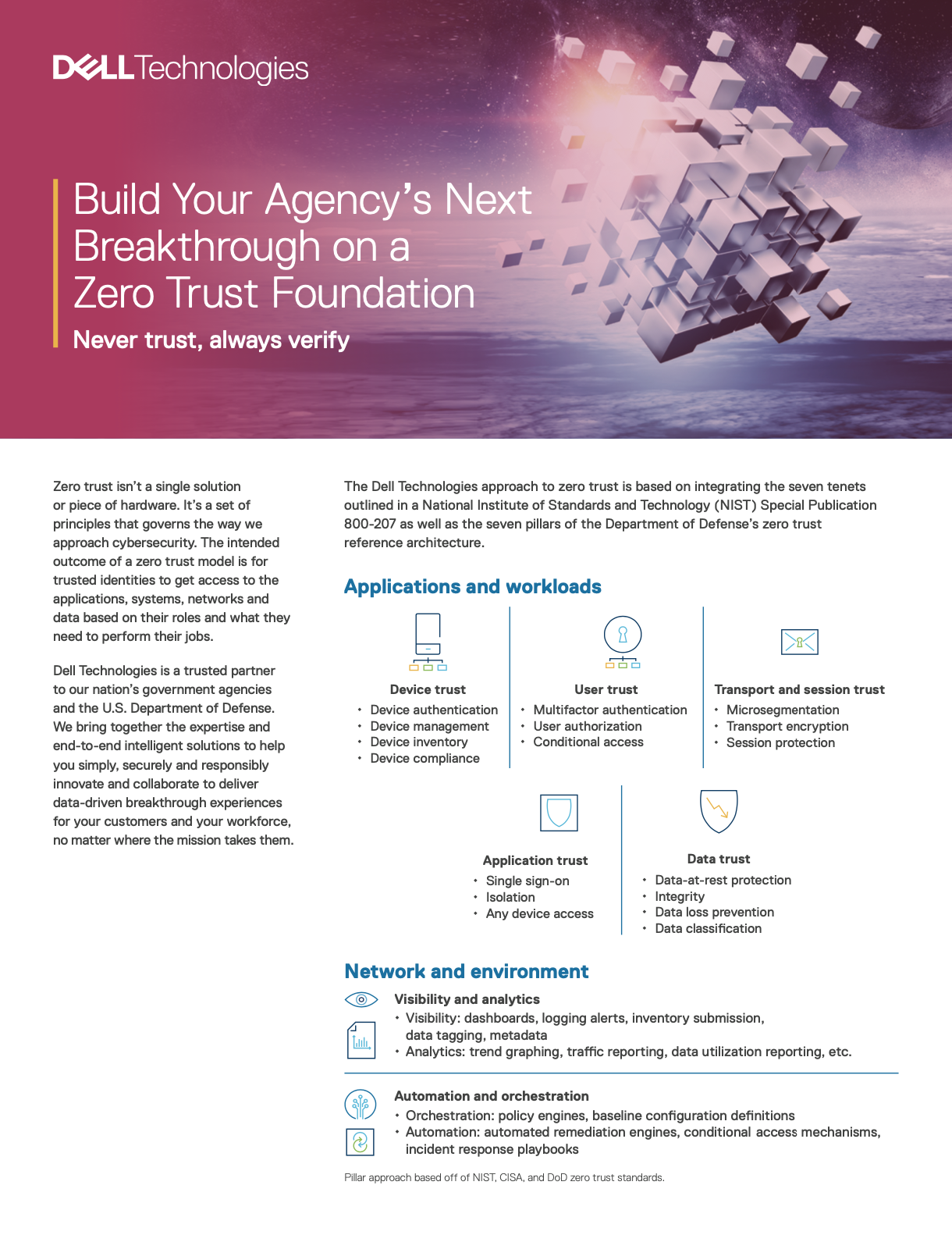
The Dell Technologies approach to Zero Trust is based on integrating the seven tenets outlined in a National Institute of Standards and Technology (NIST) Special Publication 800‑207 as well as the seven pillars of the Department of Defense’s Zero Trust reference architecture.


.png)